Mitigating Supply Chain Attacks - Bitdefender TechZone
2026-05-13
Third-party involvement drove 30% of 2025 breaches. GravityZone closes the trusted-vendor blind spot with behavioral verification across ATC, PHASR, and EDR/XDR — stopping supply chain compromise before it becomes a downstream liability.
Modern organizations do not operate in isolation, and a single compromised open-source library can disrupt operations across hundreds of organizations worldwide. Business operations depend on a broad ecosystem of third-party components and services, including software and hardware suppliers, cloud providers, and managed service partners. This interconnectedness, while enabling functionality and scalability, introduces inherent security vulnerabilities.
The Verizon Data Breach Investigations Report (DBIR) 2025 indicated that third-party involvement was a factor in 30% of all breaches, a significant increase from 15% reported in 2024.
In the supply chain, you may not be the final target, but you are still a potential attack vector. Your security posture directly affects your partners. If your systems are compromised, attackers can leverage your established trust relationship to move downstream and breach your customers or partners.
This whitepaper analyzes the technical characteristics of supply chain attacks and provides practical mitigation strategies.
Understanding Supply Chain Attacks
Supply chain attacks are diverse, leveraging various methods to compromise an organization through its trusted external dependencies. These attacks can be categorized by their primary target and method of exploitation:
Software Supply Chain Attacks: Involve the compromise of software components or distribution mechanisms. Examples include the injection of malicious code into open-source libraries, or the tampering of software updates. Once compromised, the malicious software is then distributed to unsuspecting customers, leading to widespread infection.
Hardware Supply Chain Attacks: Involve tampered or counterfeit hardware introduced during manufacturing, transit, or distribution.
Compromise of Third-Party Vendor: Involve attacks that directly target external entities (vendors, service providers, partners, contractors) on which an organization relies, focusing on either their personnel or their operational infrastructure.
The Dual Role: Victim or Entry Point
In the supply chain, your organization never exists in a silo. It acts as an interconnected node that can serve as either a threat destination or the entry point to another entity. While these relationships are often viewed vertically (upstream/downstream), supply chains are complex ecosystems where threats also move laterally through partners, shared service integrations, or federated identities.
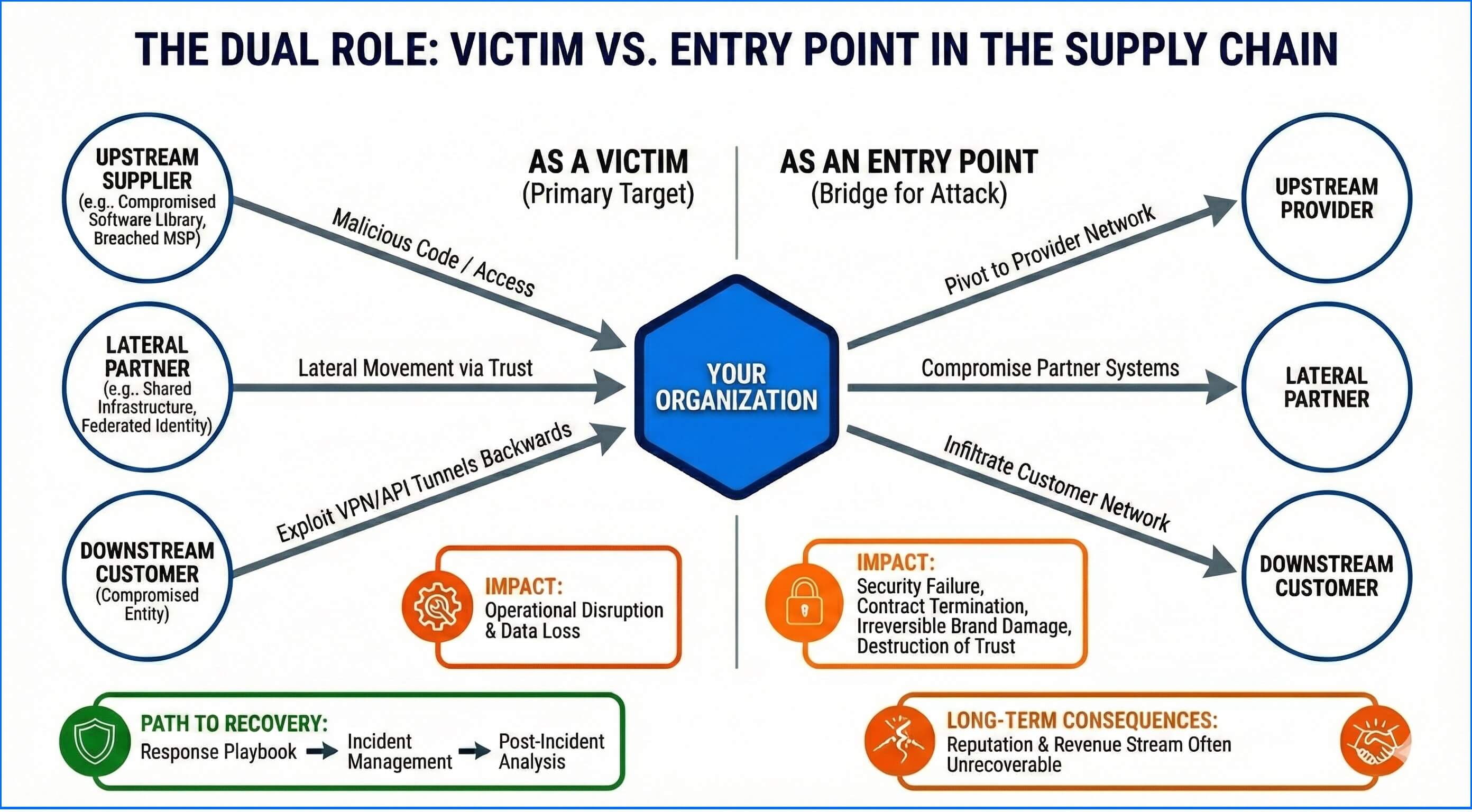 |
As a Victim: Your organization is the primary target. The attack originates from an external entity within your ecosystem. While this is commonly an upstream supplier (e.g., a compromised software library or a breached MSP), it can also be a lateral partner with shared infrastructure or even a downstream entity (customer) that has been compromised to reach your environment—often by exploiting trusted communication channels or administrative access. For example, an attacker may compromise a downstream customer to exploit VPN support tunnels or abuse authorized API keys that connect back to your internal infrastructure. While the operational disruption and data loss can be significant, the path to recovery is often defined by a response playbook, incident management, recovery, and post-incident analysis.
As an Entry Point: Your organization becomes the bridge for an attack on another entity. Attackers exploit your vulnerabilities to pivot into the networks of your customers, partners, or even providers. In this scenario, you are the security failure that your customers' security teams warned their board about. For many organizations, this results in the permanent termination of key contracts and irreversible damage to the brand. If your business relies on a major partner, a breach facilitated by your systems doesn't just damage your data; it destroys the foundational trust required to do business. While a victim can recover their systems, an entry point may never recover their reputation or their revenue stream.
Supply Chain Attack Profiles
The impact of a successful supply chain attack frequently scales beyond the initial point of compromise, resulting in systemic operational failures and deep reputational damage. The technical profile of these incidents generally falls into two categories based on their movement and scale:
High-Frequency, Rapid-Lateral Movement Incidents: These attacks prioritize volume and speed, typically targeting the "weakest link" in the ecosystem—smaller service providers or partners with expansive access but limited defensive resources. Once an initial foothold is established, attackers leverage discovery tools to move laterally through trusted tunnels (VPNs, shared storage, or federated SaaS environments). By exploiting these established trust relationships, they utilize trusted connections—often originating from unmanaged devices that sit outside the organization's direct control—to move laterally into high-value targets, often compromising multiple downstream entities simultaneously.
Low-Frequency, High-Impact Software Compromises: These are sophisticated, long-term operations targeting the integrity of the software development lifecycle (SDLC). By compromising a single core component, a build server, or a signing certificate, attackers can inject malicious payloads into legitimate distribution channels. Because the malware is delivered via trusted update mechanisms, it bypasses traditional perimeter defenses that rely on implicit trust or vendor whitelisting. Many security solutions prioritize performance over security by exempting trusted vendors from deep scanning, creating a blind spot. In contrast, Bitdefender Advanced Threat Control (ATC) operates on a zero-trust execution model, monitoring all processes and their states in real-time. This ensures that even "trusted" applications are blocked if they exhibit malicious behavior, preventing immediate, global reach across the entire user base of the affected software.
Supply Chain Risk Assessment
Effective mitigation requires integrating Cyber Supply Chain Risk Management (C-SCRM) across the organization. Unlike general risk frameworks, C-SCRM addresses the unique risks of external dependencies throughout the product and service lifecycle. This continuous analytical process involves:
Dependency Mapping: Systematically inventory all third-party software (via Software Bill of Materials - SBOM), hardware provenance, and service providers. This establishes the full scope of potential external "entry points" and identifies unmanaged assets or "shadow" dependencies that bypass corporate procurement and security review. High-fidelity asset inventories enable rapid cross-referencing between emerging Common Vulnerabilities and Exposures (CVEs) and the current runtime state of the environment. As the window between vulnerability disclosure and active exploitation continues to shrink—particularly for edge infrastructure—maintaining exact versioning data enables automated patch prioritization based on real-time threat intelligence.
Adversary Profiling: Analyze threat actors specifically targeting your vendor ecosystem or industry-standard software. Third-party risks have become a primary catalyst for the explosion of modern threats like ransomware, as vendors are frequently the "weak link" leading to mass disclosures of customer data. Supply chain attacks that compromise software development cycles or "one-to-many" delivery services have wreaked havoc across global industries, utilized by both criminal and nation-state threat actors. To defend against these methodologies - such as build-system compromise or "watering hole" attacks - Bitdefender MDR Plus provides proactive monitoring of vendor-specific attack vectors. This tier integrates managed threat modeling to analyze specific supplier dependencies, providing technical validation of potential attack paths before they are leveraged in a live environment.
Supply Chain Vulnerability Assessment: Evaluate the security posture of partners and the integrity of their deliverables. The focus is on identifying "upstream" weaknesses, such as insecure CI/CD pipelines, lack of multi-factor authentication for administrative access, or unvetted open-source libraries. This assessment must also account for the security of devices used by third-party contractors to access your environment. Bitdefender MDR Plus customers can disclose these critical third-party relationships through their customer onboarding questionnaire, which is integrated into a custom threat model for persistent intelligence monitoring. Furthermore, Cyber Threat Intelligence (CTI) monitoring includes active surveillance for sensitive data or credentials that may be exposed on public code repositories, paste sites, and criminal marketplaces.
Compliance and Governance Mapping: Align vendor assessments with regulatory requirements (e.g., NIST 800-161, NIS2, or SOC2). This ensures that third-party risk management is not just a technical exercise but a documented component of the organization's legal and ethical governance framework.
Continuous Monitoring Integration: Pivot from periodic assessments to the integration of real-time threat intelligence and vendor-related telemetry. This enables security analysts to detect anomalous behavior within a trusted partner's infrastructure and respond before a full ecosystem compromise occurs.
Systemic Impact Analysis: Quantify the "blast radius" of a partner's compromise. This measures how a breach at a supplier translates into operational downtime, data loss, or cascading failures. It specifically evaluates how a "trusted" lateral pivot could lead to the compromise of high-value internal assets.
Strategic Mitigation (Risk Response): Implement technical and procedural controls to limit third-party exposure. This includes enforcing "least privilege" for vendor access, hardening build environments, and codifying strict security requirements in Service Level Agreements (SLAs). Technical responses should prioritize moving away from implicit trust toward behavioral monitoring of all third-party interactions, including automated de-provisioning of access upon contract termination.
Establishing Controls: A Multi-Layered Security Strategy
While preventing every supply chain attack vector is impossible, organizations can significantly reduce their attack surface through proactive preventative controls. Effective strategy relies on a continuous transition from assessment to active protection, aligned with the Defense-in-Depth model.
A resilient defense starts with Bitdefender Risk Management. By providing runtime verification of managed endpoints, Risk Management transforms vulnerabilities into actionable remediation tasks. This layer eliminates known misconfigurations that attackers exploit for initial access and streamlines the patching of vulnerable software to shrink the available attack surface. By resolving these fundamental security gaps, Risk Management establishes a stable foundation for the two primary pillars of supply chain defense: safeguarding upstream software integrity and securing third-party interactions.
Safeguarding Upstream Integrity
Traditional security relies on "signed" software and "trusted" vendors. However, supply chain attacks prove that even legitimate, digitally signed updates can carry malicious payloads. Safeguarding the upstream chain requires a transition from identity-based trust to behavior-based verification, implementing Zero Trust at the process level. We must assume that any piece of software—regardless of its origin—could be compromised before it reaches the endpoint. As established in earlier sections, many security solutions prioritize performance over security by exempting trusted vendors from deep scanning, creating a critical blind spot. To close this gap, organizations must implement rigorous, non-discriminatory validation that treats all incoming traffic and artifacts as potentially hostile until proven otherwise by their operational behavior.
Advanced Threat Control (ATC) provides the necessary layer of constant suspicion. It does not stop its inspection once a program starts; instead, it monitors the process for its entire lifecycle, treating every "trusted" update as if it were on a permanent probationary period. Utilizing over 300 heuristics and real-time machine learning, ATC tracks the sequence of events—every system call, API interaction, and file change. If a legitimate application suddenly begins to exhibit anomalous behavioral patterns—such as SAM registry dumping, suspicious credential access, or unauthorized process injection—ATC identifies the risk immediately. By assigning a behavioral probability score to these actions in real-time and terminating the process once a threshold is reached, ATC ensures that a compromised vendor update cannot hide behind a valid digital signature.
Due to its deep telemetry, ATC is frequently the core technology utilized in Bitdefender security advisories to document zero-day exploits and high-profile supply chain attacks. This telemetry provides the forensic depth required to deconstruct complex attack chains, which are regularly shared with the security community via the Ctrl-Alt-DECODE (you can subscribe for technical deep-dives).
True resilience requires looking even deeper than the operating system. Process Introspection (PI) provides deep protection by monitoring memory-state changes and key process operations from a low-level perspective. Many supply chain attacks use "fileless" methods to avoid detection, attempting to hide their movements by manipulating the memory of trusted programs via techniques like process hollowing or DLL side-loading. Process Introspection identifies these "turncoat" processes by applying advanced security checks during module loading and thread creation. Because it operates primarily in kernel mode, PI is resilient against user-mode evasion techniques like DLL unhooking. It detects when a program tries to subvert its own memory space or inject malicious instructions into another process, even if the malware manages to gain administrative rights.
To illustrate this synergy: in the event of a compromised browser update, ATC monitors the resulting sequence of events and terminates the process if it initiates malicious actions like unauthorized credential dumping. Simultaneously, PI monitors the internal integrity of the process to detect malicious state changes—such as process hollowing—regardless of the specific evasion technique employed. The result is overlapping protection, ATC neutralizes the threat based on its malicious behavior, while PI stops it because the underlying memory state has been compromised. This combination ensures that "trusted" software remains truly safe.
Bitdefender MDR integrates Cyber Threat Intelligence (CTI) and Security Operations Center (SOC) analysts to neutralize supply chain risks. Using customer onboarding questionnaires—where clients provide a detailed inventory of known applications and software—as a foundational baseline, the CTI team incorporates data on widespread vulnerabilities targeting popular platforms and risks identified via internal SOC telemetry to provide technical advisories that outline affected versions, workarounds, and direct links to vendor updates. Additionally, this intelligence is integrated into Risk-Based Threat Hunting packages used by the SOC team to ensure that identified vulnerabilities before they can escalate.
Securing the Connected Business Ecosystem and Third-Party Interactions
Beyond software, the supply chain includes the human and operational infrastructure of third-party vendors. Attackers often bypass hardened perimeters by targeting the "side doors" provided to contractors or service providers. The primary danger of such a breach is the "Day Zero" invisibility of the adversary; because they enter through verified channels—such as Site-to-Site VPNs or administrative portals—they appear as legitimate technicians performing authorized tasks. In this scenario, the supply chain compromise acts as a specialized tactic to gain an initial foothold, where post-exploitation steps—such as internal reconnaissance and privilege escalation—are masked by authorized access. Because static identity checks alone cannot differentiate between a valid user and a threat actor inheriting this level of trust, transitioning to continuous behavioral monitoring is the only viable defense to detect subtle deviations from established baselines.
When an attacker leverages a trusted tunnel to enter the environment, their next objective is lateral movement. Bitdefender Network Attack Defense provides a critical layer of visibility into this phase. By monitoring endpoint-level network traffic, it can discover and block scans and lateral-movement techniques—such as brute-force attempts on internal services or exploitation of network protocols—that an adversary uses once they pivot from the initial entry point.
To further complicate an attacker's movement, organizations must systematically shrink the internal attack surface by neutralizing the tools adversaries rely on. Proactive Hardening and Attack Surface Reduction (PHASR) enables security teams to block "Living off the Land" (LOL) binaries, legitimate system tools, and applications that fall outside a specific user's role or the machine's intended function. By leveraging behavioral profiles that map authorized tasks to specific toolsets, PHASR creates a restrictive environment where an attacker’s inherited "trust" does not grant them a functional toolkit. This strips away their stealth, forcing them to employ noisier, non-standard methods that are far easier to detect.
While hardening restricts options, sophisticated actors may still attempt to "blend in" using hijacked administrative credentials. To expose these subtle deviations, Bitdefender EDR and XDR serve as the detection engine, utilizing sensors across Endpoint, Network, Cloud, and Identity layers to correlate telemetry. This approach functions as a behavioral explainer, connecting seemingly unrelated events into a logical attack sequence. By transforming "legitimate" sessions into incidents, it enables automatic remediation to block threats and guided manual investigation to neutralize the root cause of the intrusion.
Because detection is only as effective as the response that follows, Bitdefender MDR addresses the critical variable of time in a supply chain attack. Adversaries exploiting a 'trusted' partner relationship often operate during off-hours or holiday windows, betting on the fact that internal security teams are stretched thin. Bitdefender MDR transforms passive defense into an active hunt, providing 24/7/365 professional monitoring where Bitdefender SOC analysts look beyond simple endpoint telemetry to understand the unique context of your business. By cataloging critical third-party dependencies during onboarding, the CTI team creates tailored threat modeling used by the SOC team for proactive hunting. With pre-approved response actions, analysts can take immediate action—such as isolating a compromised machine—the moment a breach is confirmed.
Incident Response and Recovery for Supply Chain Attacks
Even with the best preventative controls and advanced detection, you must assume attackers can still breach your supply chain. Robust incident response and recovery capabilities are therefore crucial to minimize damage, restore operations, and maintain trust. Because organizations often lack comprehensive visibility into the security posture of third-party vendors, incident response plans must incorporate a ‘trust but verify’ approach to continuously validate their security status.
Architectural Readiness and Response Playbooks
Resilience in the face of a supply chain compromise depends on the transition from ad-hoc troubleshooting to pre-defined, technical workflows. Because these attacks often leverage authorized administrative tunnels or signed software, the response must be meticulously prepared and regularly exercised.
Bitdefender Event Preparedness services provide the technical framework for developing these capabilities. By analyzing specific supply chain attack paths—such as a compromised Managed Service Provider (MSP) or a poisoned CI/CD pipeline—organizations can build step-by-step response playbooks. These playbooks outline specific roles, communication protocols, and containment actions, ensuring that SecOps teams act decisively rather than spending critical minutes during the "Golden Hour" of an incident defining their strategy.
Recovery via Verified Integrity and Secure Re-provisioning
Containment is only the first phase of the response lifecycle. The high-risk nature of supply chain attacks—where malware may be embedded in legitimate updates or hardware—requires a recovery process focused on comprehensive restoration to a verified state. Successful recovery depends on Isolated Backup Verification, where restoration utilizes immutable, offsite backups scanned for indicators of compromise (IoCs) before deployment. This technical gate prevents the "re-infection loop" where an attacker’s dormant payload is restored alongside legitimate data.
In the event of a compromised software delivery mechanism, Secure Re-provisioning through Golden Images is utilized because simply patching the existing environment is insufficient. Organizations utilize these verified, hardened system templates to re-provision affected infrastructure, guaranteeing that any persistent artifacts or unauthorized configuration changes introduced by the adversary are completely purged. Every incident must conclude with a rigorous Post-Incident Root Cause Analysis (RCA). This technical autopsy identifies how the supply chain vulnerability was exploited, assesses the performance of current detection layers like Advanced Threat Control (ATC), and feeds these insights back into the risk assessment cycle to harden the environment against similar vectors.
Technical Reporting and Regulatory Communication
Supply chain incidents frequently trigger legal and contractual obligations that require transparent, high-fidelity reporting.
A pre-approved communication plan is essential for maintaining trust with partners and customers. This plan must define the technical criteria for breach notification, as required by global regulations. By involving legal counsel early in the preparation phase, organizations can define their liability and ensure that reporting to media and regulatory bodies is controlled, accurate, and timely. This structured approach transforms a potential reputational catastrophe into a documented demonstration of security maturity and professional governance.
Conclusion
Supply chain attacks represent the most complex architectural threats facing modern organizations. Their multifaceted nature—extending from compromised open-source libraries to exploited third-party administrative access—underscores the reality that no entity functions in isolation. Defending these interconnected nodes requires moving beyond static perimeter security toward a continuous model of behavioral verification.
While no organization is immune to ecosystem-wide vulnerabilities, resilience is achieved through a multi-layered strategy that integrates proactive risk assessment, automated preventative controls, and high-fidelity detection. Technologies such as Bitdefender EASM, Risk Management, PHASR, and ATC establish the necessary visibility to eliminate misconfigurations and block malicious execution. Complementarily, EDR, XDR, and MDR provide the correlation and expert monitoring required to neutralize lateral movement originating from trusted channels. By operationalizing scenario-specific playbooks and maintaining readiness for transparent communication, organizations can minimize the operational impact of a breach and preserve the foundational trust required for modern business operations.