What is Bring Your Own Vulnerable Driver (BYOVD) – Bitdefender TechZone
BYOVD attacks weaponize legitimate, signed drivers to gain Kernel Mode (Ring 0) privileges. See how threat actors bypass Windows Driver Signature Enforcement to disable security tools and execute code with maximum system authority.
As EDR and XDR solutions have become standard in modern environments, threat actors have adapted their tactics to either remain undetected through "Living off the Land" (LotL) techniques or to actively disable security agents. To achieve the latter, they frequently use the Bring Your Own Vulnerable Driver (BYOVD) technique.
While gaining administrator privileges allows an attacker to control many aspects of a machine, it does not grant them absolute control. Modern security solutions operate at the deepest level of the operating system, the kernel. To disable, bypass, or "blind" these solutions, an attacker must escalate their privileges from Administrator (User-Mode) to System (Kernel-Mode).
In the Windows security model, the kernel is the most protected layer. To prevent malicious code from executing at this level, modern 64-bit versions of Windows require all drivers to be digitally signed by a trusted authority. BYOVD allows attackers to bypass this gatekeeping by leveraging legitimate, signed drivers that contain security flaws.
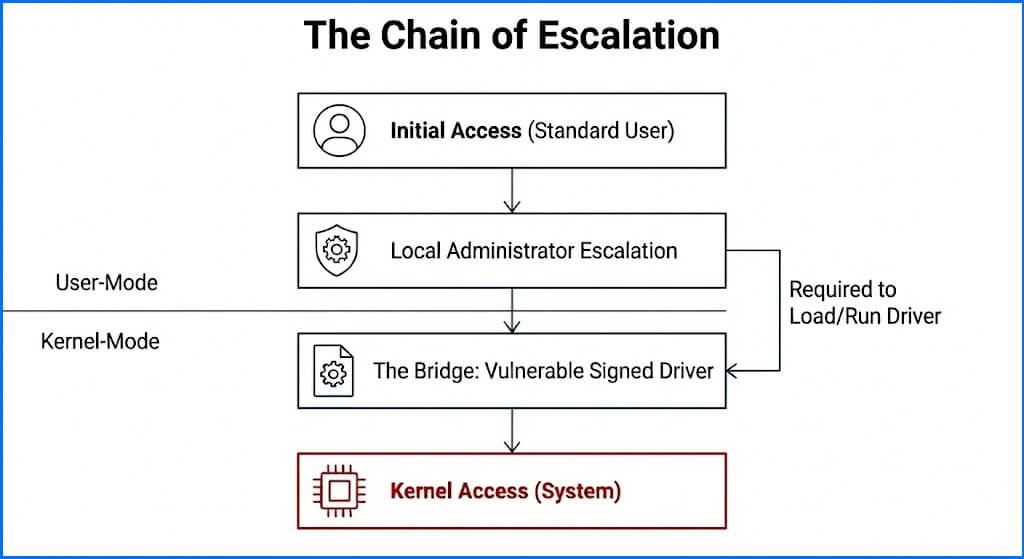
The Chain of Escalation
The use of BYOVD is typically the final stage in a multi-step chain of escalation. Attackers often begin their journey with a standard user account, gained through methods like phishing or credential theft. Because a standard user is heavily restricted by the operating system, the first objective is to escalate to a local administrator account. This transition allows the attacker to modify system settings and manage services, but it still limits them to User-Mode.
To tamper with endpoint security solutions, the attacker must bridge the gap between User-Mode and Kernel-Mode. Drivers serve as the primary bridge for this escalation, as they are the only components authorized to execute code within the kernel. Windows strictly limits the ability to load or unload device drivers to the SeLoadDriverPrivilege, which is reserved for Administrators and the System account. However, even as administrators, attackers cannot simply load their own custom malicious drivers because they lack a valid digital signature from a trusted authority.
To overcome this hurdle, attackers look for pre-existing, trusted drivers that are either vulnerable to exploitation or provide unsafe functionality by design. By "bringing" these legitimate drivers to the system and loading them using their administrator rights, they create a bridge to the kernel-mode. Once they are in the kernel, attackers have numerous options to directly attack the security agent and its monitoring capabilities.
 |
How BYOVD Works
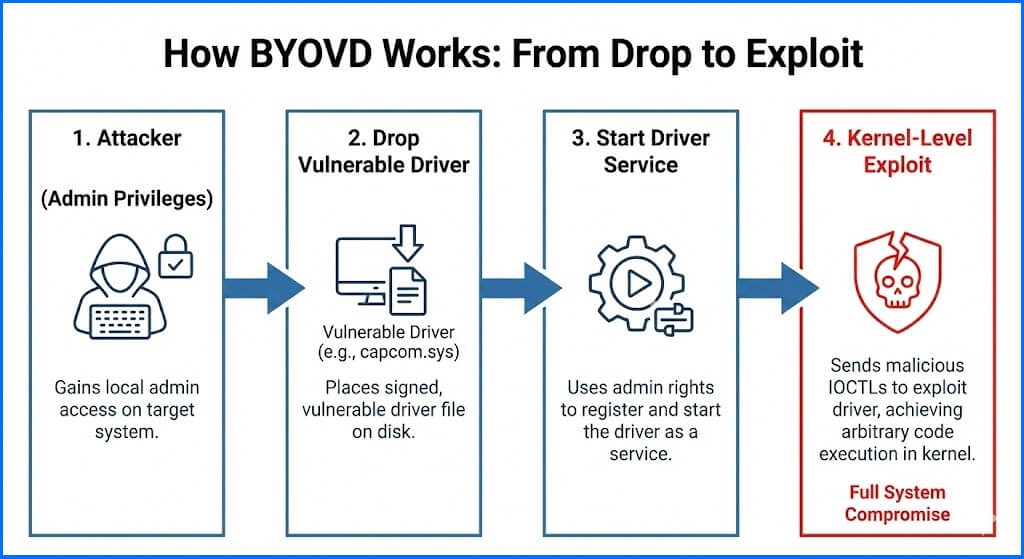
The goal of a BYOVD attack is to gain kernel-mode privileges, often called Ring 0. At this level, code has unrestricted access to system memory and hardware. Since an attacker cannot load an unsigned malicious driver, they "bring" a driver signed by a reputable vendor (such as a hardware manufacturer or an old antivirus version) that has a known vulnerability.
Initial Access and Elevation: The attacker first gains administrative rights on the target machine. While administrators have significant power, they still operate in user-mode. To move to the kernel, they must load a driver.
Dropping the Driver: The attacker places a known vulnerable driver on the disk. These are often outdated versions of motherboard utilities, GPU tools, or diagnostic software.
Loading the Driver: Using administrative privileges, the attacker installs and starts the driver service. Because the driver has a valid digital signature, Windows allows it to enter the kernel.
Exploitation or Abuse: Once the driver is running in the kernel, the attacker sends Input/Output Control (IOCTL) commands to it. They either exploit a bug (like a buffer overflow) to execute shellcode, gain arbitrary memory access (read/write), or use "insecure by design" features to manipulate system memory.
 |
The Driver Lifecycle
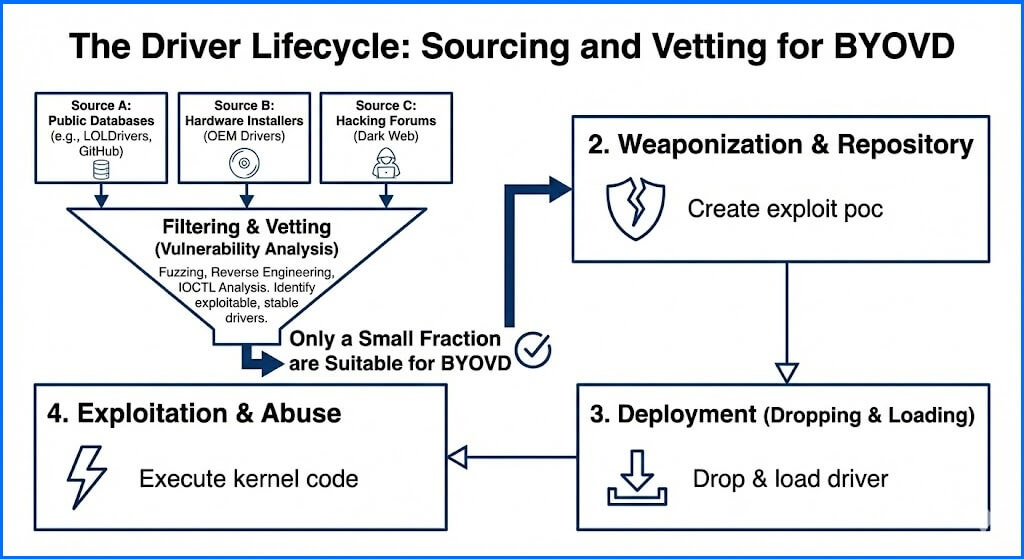
The effectiveness of this technique relies on the attacker's ability to source the correct files. Not every driver is a candidate for BYOVD. For a driver to be useful, it must allow a user-mode application to trigger a kernel-mode action exceeding its intended scope.
Threat actors find these drivers through proactive methods. They monitor public security research and databases like "LOLDrivers," which catalog signed drivers known to be abusable. They also perform "driver hunting" by scanning large volumes of legitimate software installers from hardware vendors for common IOCTL vulnerabilities. Once a driver is identified, it is added to a repository of pre-signed exploits.
Attackers often prefer legacy drivers from the 2013 to 2016 era because they lack modern security features like Control Flow Guard (CFG), making them easier to exploit. Simultaneously, they scan brand new software releases, as newly discovered drivers are highly valuable because they are not yet included in any blocklists, providing a window of opportunity before security vendors can react.
Beyond abusing legitimate drivers, Bitdefender Labs has investigated cases involving purposefully designed malicious drivers. In these scenarios, threat actors develop custom malware from the ground up to operate specifically within the kernel. To bypass certification requirements, they use stolen digital certificates obtained from legitimate vendors who have suffered data breaches. In these instances, the primary remediation is for the certificate authority to revoke the stolen certificate entirely, rather than adding individual driver hashes to a blocklist.
 |
Vulnerability vs. Permissive Design
There are two primary ways a driver can enable a BYOVD attack. Vulnerable drivers contain coding errors that an attacker exploits to execute arbitrary code within the kernel. A well-known example is capcom.sys, a driver for the game Street Fighter V. This driver contained a functionality that intentionally disabled Supervisor Mode Execution Prevention (SMEP) to allow the execution of user-provided code in the kernel. This "feature" was intended as a protective anti-cheat measure but essentially provided a signed, open door for any attacker with administrator privileges.
Permissive or "Insecure by Design" drivers function exactly as intended by their developers but expose dangerous capabilities to user-mode applications. Drivers designed for hardware monitoring or low-level system access, such as winio.sys, often provide direct read and write access to physical memory (RWPM). Drivers in this category often include functionality that allows a user-mode application to map physical memory via kernel functions like MmMapIoSpace. Another common example is the RTCore64.sys driver from MSI Afterburner, which has been repeatedly abused by ransomware groups like BlackCat. These drivers are not necessarily "buggy." Instead, they provide legitimate features that an attacker can repurpose to manipulate kernel structures, such as process lists or security callbacks, without needing a traditional exploit.
The Spectrum of BYOVD Impact
Since you’ve learned the mechanics of how a driver is targeted (bugs vs. design), we can now analyze what the consequences are. BYOVD is a generic term that covers a variety of scenarios. The potential for damage depends entirely on the specific capabilities of the driver being abused. These capabilities generally fall into two categories.
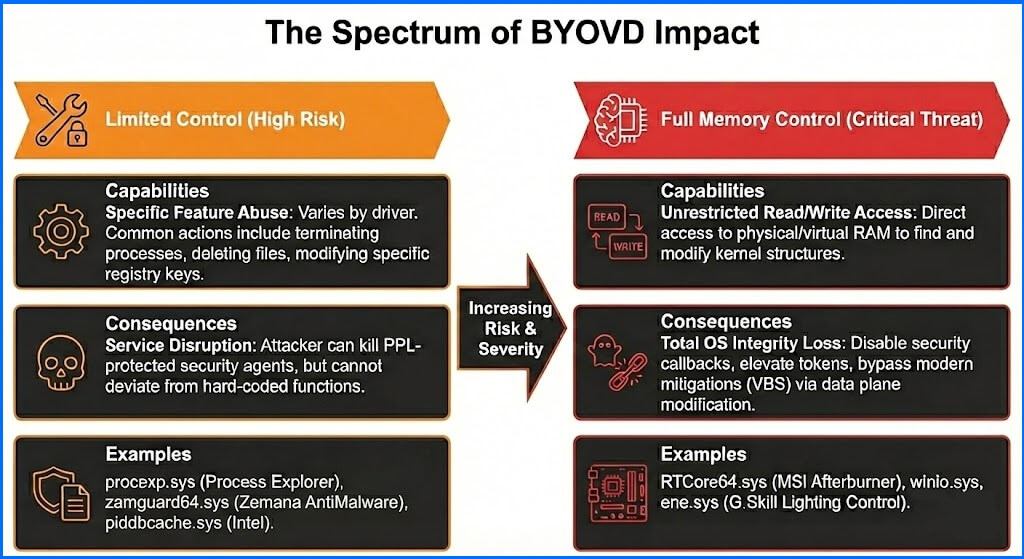 |
Limited Control
The first category involves drivers that expose specific features that don’t offer full memory access, but provide functionality that serves the attacker's needs. For example, a driver (such as procexp.sys for Process Explorer) might include a legitimate function to terminate system processes. While this is useful for diagnostic tools, an attacker can use it to kill the security agent's process. This is the less severe form of BYOVD impact because the attacker is limited to the specific functions the developer included in the driver.
Antimalware and antirootkit tools, such as the Zemana AntiMalware (ZAM) driver, deserves a special mention. Unlike hardware drivers, these are designed for disinfection and must expose kernel-level functions to terminate processes or delete files. Threat actors use tools like Terminator to abuse these IOCTLs, which often ignore Protected Process Light (PPL) flags that normally safeguard security agents. By using these specialized drivers, an attacker can kill an EDR agent even when standard administrative tools would be blocked.
Full Memory Control
The second, more dangerous category includes drivers that provide unrestricted access to kernel memory. These are often hardware-related drivers designed to allow low-level system configuration. When abused, they allow an attacker to read from or write to any part of the system's RAM.
This is significantly worse than targeted feature abuse because protecting every single bit of the system's memory is nearly impossible. There are billions of critical memory bits, many of which are poorly documented or change dynamically. By modifying a few bytes, attackers can disable security callbacks, elevate their own process tokens, or hide malicious artifacts. Because these modifications occur in the data plane rather than the execution plane, they are nearly impossible to block without a massive, system-wide performance penalty. Once an attacker has full memory control, the operating system's integrity is effectively non-existent.
You might be surprised why the arbitrary code execution is not ranked as high as the read/write access to the memory. Unrestricted memory access is technically more dangerous and difficult to defend against in a modern Windows environment. Microsoft has introduced effective hardware-based mitigations to stop code execution, such as Virtualization-Based Security (VBS) or HVCI (HyperVisor-protected Code Integrity), which make it difficult for an attacker to inject and run new code in the kernel.
Consumer vs. Business Security Products
The effectiveness of a BYOVD attack often depends on the type of security product installed. There is a significant difference in how consumer antivirus and enterprise EDR solutions handle anti-tampering. Consumer products often prioritize software compatibility to ensure that games, anti-cheat drivers, and performance overlays work without interruption. Modern gaming titles frequently include kernel-level anti-cheat systems, such as Riot Vanguard or BattlEye, which operate at the same privilege level as the security agent.
A compatibility problem arises because both the anti-cheat system and the security agent want to monitor the same sensitive kernel functions. When two different drivers attempt to "hook" or redirect the same system call at the same time, it can lead to immediate system instability or a Blue Screen of Death (BSOD). Aggressive anti-tampering features might also view the anti-cheat system's attempts to protect game memory as a malicious attack. To avoid the frequent system crashes or software blocks that would alienate home users, these products are often designed with a more permissive stance toward low-level kernel interactions.
This distinction is important because many public "EDR bypass" demonstrations utilize consumer products to showcase successful attacks. While these demonstrations are effective for educational purposes, they often fail to represent the reality of a modern enterprise environment. Consumer products lack the hardened self-protection mechanisms found in business-grade solutions, making them easier targets for termination or blinding.
Business-grade solutions, such as Bitdefender GravityZone, include specialized features, such as kernel-level hooks and callback monitoring, that are far more difficult for an attacker to bypass. In a business environment, if a security agent blocks a legitimate but vulnerable driver, an administrator can investigate and create an exclusion. In the consumer world, the user would often simply blame security software and uninstall it.
How to Protect Against BYOVD Attacks
To understand why defending against BYOVD is difficult, it is necessary to look at the mechanisms intended to manage digital trust. A Certificate Revocation List (CRL) is a publicly accessible database maintained by a Certificate Authority (CA). It contains a list of digital certificates that have been cancelled before their scheduled expiration date. CRLs are not specific to drivers. They are used to manage trust for websites, encrypted communications, and software across the entire internet. When a system attempts to load a signed driver, it is supposed to check the CRL to ensure the certificate used to sign that driver is still considered valid. If the certificate appears on the list, the system should refuse to load the file.
The use of CRLs appeared to be a strong theoretical solution when the digital signing model was first established. The intent was to provide a mechanism where a compromised or vulnerable certificate could have its trust pulled by the issuing authority. However, as digital certificates became more common, CRLs began to act as a significant performance and practical bottleneck. CRL files are often non-atomic and grew to sizes that caused latency during every signature check on the system. Because a single CRL can contain thousands of entries, parsing the list in real-time is computationally expensive. Furthermore, Windows is unable to check CRLs during the boot process because network connectivity is not yet established. These issues led many administrators to disable CRL checks entirely to prevent system instability.
While CRLs remain part of the Windows security architecture, they are now treated as a worst-case scenario option rather than a primary defense. Microsoft has shifted toward the Vulnerable Driver Blocklist as a more practical and targeted strategy. This approach allows the operating system to block specific file hashes of known-bad drivers without the broad, destructive impact of revoking an entire vendor certificate. Since the Windows 11 2022 update, this blocklist has been enabled by default. It provides a more agile response to the BYOVD threat because new hashes can be distributed through standard Windows updates without requiring the coordination needed for a full certificate revocation.
Bitdefender GravityZone Protections
Bitdefender GravityZone implements several specialized layers to counter BYOVD, even if a driver successfully loads.
Early Launch Anti-Malware (ELAM): The Bitdefender ELAM driver starts during the boot process before other third-party drivers, allowing it to inspect and block malicious drivers before they can establish a foothold.
Antimalware Engines and Blocklisting: The first line of defense is a comprehensive database of malicious and vulnerable driver signatures that stops the "drop" phase of the attack. Microsoft’s blocklist is typically updated only twice each year, we update signatures dynamically as soon as new vulnerable drivers are discovered.
Callback Evasion (CBE): This technology monitors the integrity of kernel callbacks. If an attacker attempts to remove or tamper with the "tripwires" that GravityZone uses for detection, CBE identifies the anomaly and alerts the security team.
Kernel Sensitive API Monitoring: GravityZone intercepts and blocks attempts to terminate processes (like using NtTerminateProcess to kill the security agent) originating from suspicious drivers.
GravityZone is one of the few security solutions that achieved the Anti-Tampering certification from AV-Comparatives, you can read more in our Anti-Tampering and Detection Evasion article.