Email Protection - Bitdefender TechZone
GravityZone integrates Extended Email Security to secure M365 and Google Workspace against BEC via post-delivery remediation. This architecture incorporates the Antispam Service for OEM partners and endpoint-level BEST sensors to neutralize malicious code.
Emails are vital for organizations, and ensuring their security is essential to protect sensitive data, maintain trust, comply with regulations, ensure business continuity, and foster a secure and productive work environment.
Unfortunately, cybercriminals often target emails due to their widespread usage, viewing them as potential gateways to infiltrate other accounts and devices. As a result, email protection is a critical component of a multi-layered security strategy, reducing an organization's attack surface.
In the present times, phishing attacks pose a significant threat to both organizations and individuals, and the adoption of AI can exacerbate this issue. AI empowers cybercriminals to craft more convincing and personalized emails, rendering them more hazardous and harder to identify compared to traditional ones. To safeguard against email account attack vectors, including phishing, spam, and ransomware, organizations can effectively eliminate a common entry point for potential attackers.
Extended Email Security
Bitdefender Extended Email Security (EES) - available through the GravityZone console side menu - provides a comprehensive suite of features designed to protect against targeted campaigns, supply chain fraud, spear-phishing, brand impersonation, and ransomware. Engineered for annually (term-based) and monthly licensed business organizations, it identifies and neutralizes threats that bypass traditional filters by providing deep mailbox visibility and post-delivery remediation.
Three Pillars of Deployment
Extended Email Security offers a modular architecture that adapts to your specific email infrastructure. You choose from three distinct deployment models to balance perimeter defense with deep mailbox visibility.
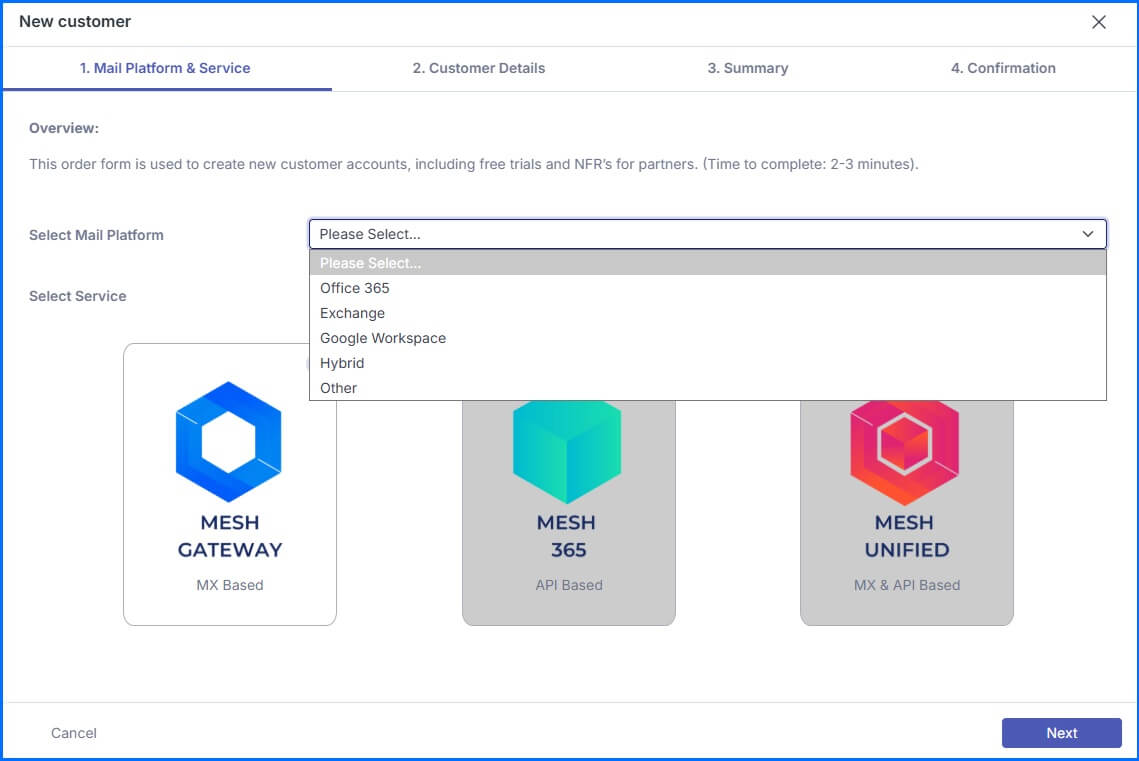 |
You can use the Gateway as a traditional Secure Email Gateway (SEG) at your network perimeter. This model is platform-agnostic. You can deploy it for Google Workspace, on-premise Exchange, or hybrid environments. You activate this by changing your domain's MX records to point to the filtering infrastructure. All inbound email routes to the gateway for filtering before it reaches your mailbox server. This approach ensures you neutralize threats before they enter your internal network. Detailed information about gateway configurations can be found at our Bitdefender Support Center here.
If you operate exclusively in a Microsoft 365 environment, you can deploy the API-based 365 solution. This product utilizes an API-only architecture and sits at the end of your security stack. You do not need to change your MX records. Instead, the service inspects the message once it has landed in the user's mailbox. This allows you to catch emails that may have passed through Microsoft's native filters or an existing third-party gateway. You complete the setup by authorizing a global admin account. This creates a secure Enterprise App within your Microsoft tenant. Detailed information about 365 configurations can be found at our Bitdefender Support Center here.
For the most comprehensive security posture, you can implement the Unified model. This combines Gateway and API capabilities into a single solution. This hybrid model is built for Microsoft 365 customers who require both perimeter protection and post-delivery remediation. You effectively eliminate your internal blind spot by monitoring both external traffic and internal communications. Your deployment requires a two-step process involving an MX record update and the authorization of the Microsoft 365 API integration. Detailed information about Unified configurations can be found at our Bitdefender Support Center here.
Configuration and Mail Flow Integration
You must perform several key configuration steps to ensure reliable mail flow within your environment. You should start by securing your incoming traffic. You create a dedicated inbound connector within the Exchange Admin Center (EAC) to restrict delivery only to messages filtered by Extended Email Security. You also establish a specific mail flow rule for the Extended Email Security IP ranges. This rule allows filtered email to be delivered safely. It also prevents potential issues caused by double filtering from Microsoft's native protection.
Next, you address your outgoing communications to maintain a sender reputation. You configure an Outbound Smarthost for Gateway and Unified deployments. This ensures that your outgoing email routes through the filtering engines. This layer protects your domain reputation and prevents your organization from being flagged as a source of spam. If you use Microsoft 365 or Exchange, you also set up an outbound filtering configuration to facilitate this secure routing.
You can also empower your users to participate in the security process through the Outlook report button. This button allows your employees to share potential false negatives or false positives directly with your helpdesk. You activate this feature by configuring settings within the Microsoft Security Center.
Visibility: The Live Email Tracker
Once your architecture is in place, you gain immediate visibility through the Live Email Tracker. This tool provides real-time telemetry for every inbound, outbound, and internal message. You can use the search interface to filter logs by sender, recipient, subject, or specific metadata.
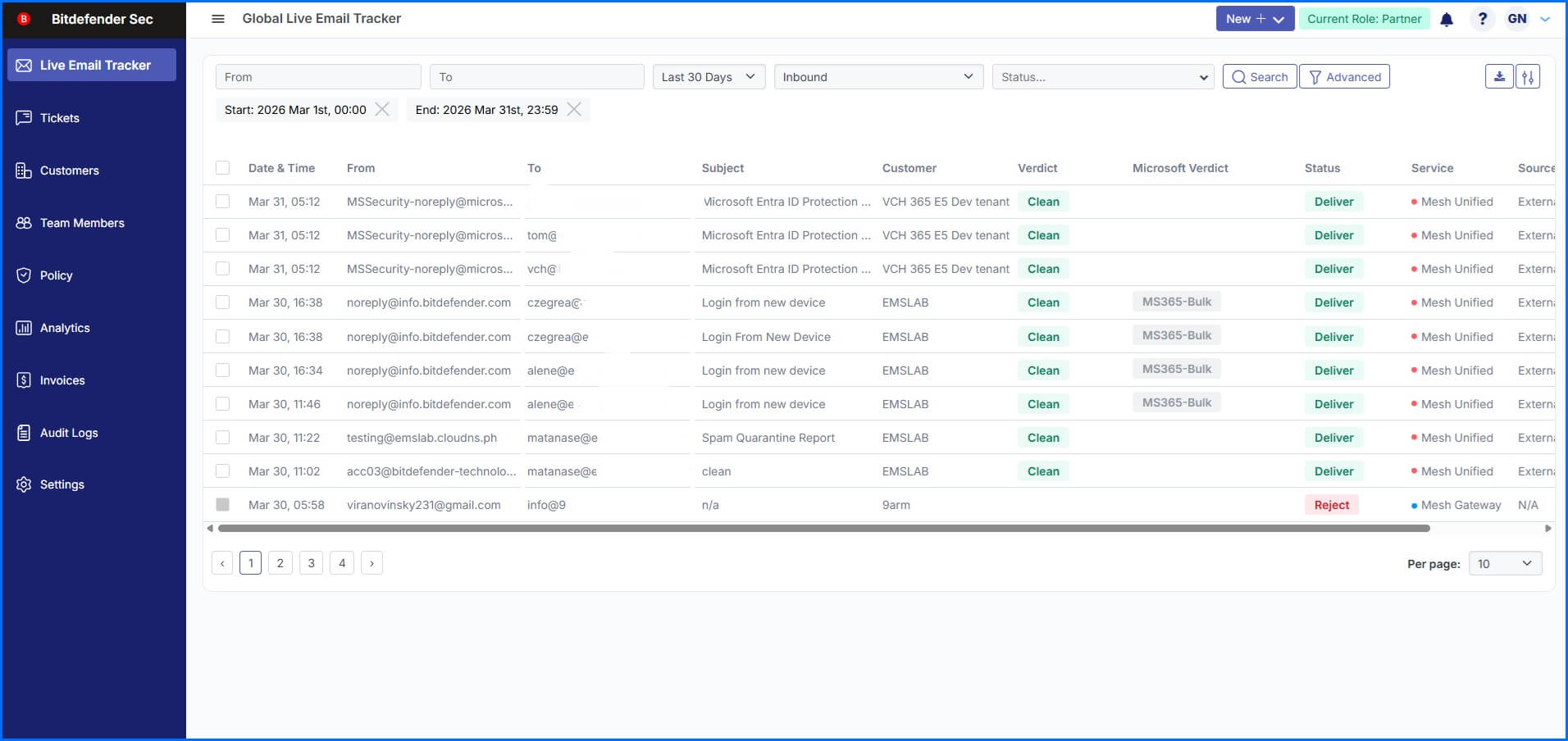 |
The system retains these detailed records for 90 days to support your forensic investigations. You can see exactly why a message was delivered or blocked by reviewing the associated verdict reasons. This high level of transparency allows you to verify security outcomes and troubleshoot delivery issues without leaving the console.
The detection engine - utilizing Bitdefender Malware Protection, Antispam and Sandbox Analyzer - stops over 99% of threats on the inbound. However, you still need tools to remediate messages that have already been delivered. This remediation capability is a key advantage if you use the 365 or Unified deployment models. Unlike the standalone Gateway, these API-integrated models allow you to trigger the Remediate action directly from the console. This process removes identified threats from the end user's mailbox. This remediation capability is not limited to a single organization; MSP partners can also execute it across multiple tenants, which provides a significant operational advantage when managing broad, customer-based incident response.
Detailed information about the Live Email Tracker, including its actions, analysis reasons, statuses, and verdicts, is available at our Bitdefender Support Center here.
You can access the tracker at three distinct levels. At the MSP Level, you maintain central visibility across all your customers. You can search for malware and phishing attempts across your entire client base at once. At the Customer Level, you view traffic specific to your individual account. At the End-User Level, users monitor traffic for their own mailboxes. You also have the option to use an API to download these records for external analysis.
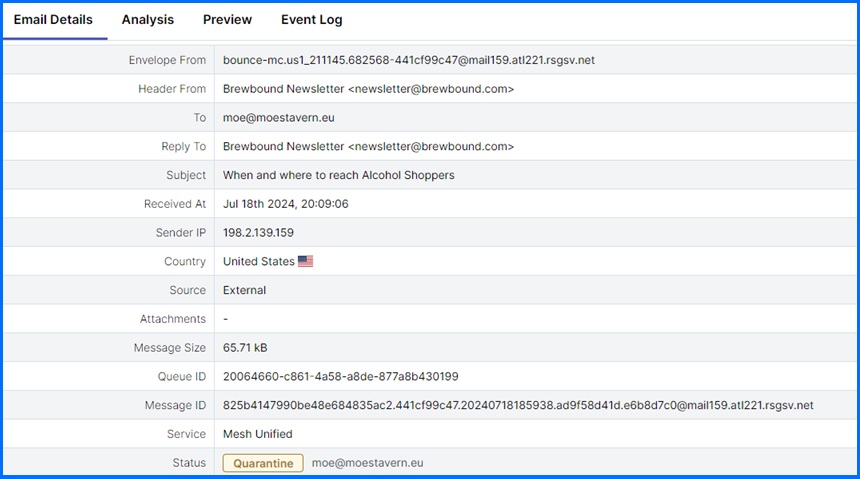 |
The tracker provides a deep technical analysis of every email. The level of visibility you receive in the tracker depends on the delivery status and the implementation type.
For example, Delivered (Clean) messages show a basic header with sender and recipient addresses, the subject line, authentication results, Message-ID and Received headers, which is essential for troubleshooting internal communication issues or identifying delivery problems. Messages with a Quarantined status provide access to full headers. This includes the complete Authentication-Results string, detailing the SPF designated sender verification, DKIM header signatures, and DMARC policy alignment. Quarantined emails also include a Preview feature that displays the email body for manual inspection of suspicious content.
Additonally, the available message statuses may depend on implementation type; for instance, 365 and Unified deployments include the Junk or Remediate statuses.
Managing Policy Templates and Rules
You can manage your policy templates globally, for a specific customer, or at the individual mailbox level to ensure the required level of granularity.
MSP Level (Global Policy Templates): You can create policy templates that apply automatically to new customers or update existing customers at scale.
Customer Level: You create policies that apply to a specific customer account.
Domain Level: You apply policies to specific domains within a tenant.
End-User Level: You create granular policies for specific mailboxes.
Configuring the Policy Template
While you configure your policy templates, you define exactly how the system responds to every scanned email. The engine assigns specific labels based on the detected intent. You assign a specific action for each verdict to automate your response. You manage outcomes for Clean, Impersonation, Infomail, Malware, and Phishing. You also control results for various Spam levels. You can set the system to Deliver, Quarantine, Reject, or take No Action. For example you might deliver clean mail by default but quarantine phishing attempts.
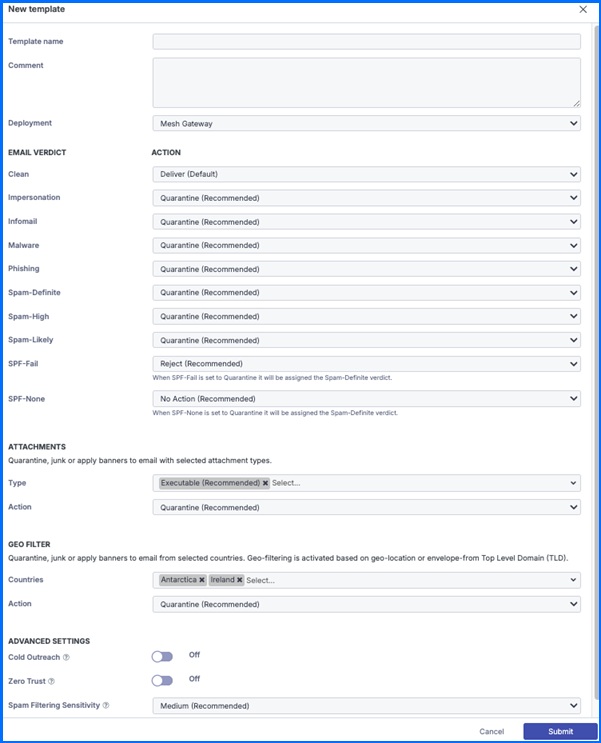 |
You further customize your security within the same template using attachment and geographic controls. You use Banned Attachments to quarantine or apply banners to specific file types. You block categories such as Executable or Encrypted files. You also manage Video, Audio, Compressed, Macros, and HTML files. You activate Geo-filtering based on physical location or the Top-Level Domain of the sender address. This allows you to block traffic from regions that your organization does not frequently contact.
The Cold Outreach toggle lets you filter unsolicited sales and marketing emails more aggressively. This is recommended for policies targeting your management teams. Zero Trust enables a quarantine by default approach. This reclassifies Clean and Infomail verdicts as Spam-Likely unless the sender is a known contact. A known contact is a sender the recipient has previously sent outbound emails to, and the system identifies these automatically for Unified and 365 models. You must use the Outbound Smarthost for the Gateway model to identify known contacts.
Finally, you adjust the Spam Filtering Sensitivity to set your threshold for spam detection. Medium is the default setting. You can set it to Low to be less restrictive, or you can choose High for maximum security across the organization or for high-risk mailboxes.
Detailed information about policy templates configurations can be found at our Bitdefender Support Center here.
Rules Management
You can create allow, block, and custom rules to bypass or override your global template configuration. These rules provide the flexibility to manage exceptions at various levels. You can apply rules globally for all MSP customers or specifically for individual accounts, domains, and mailboxes.
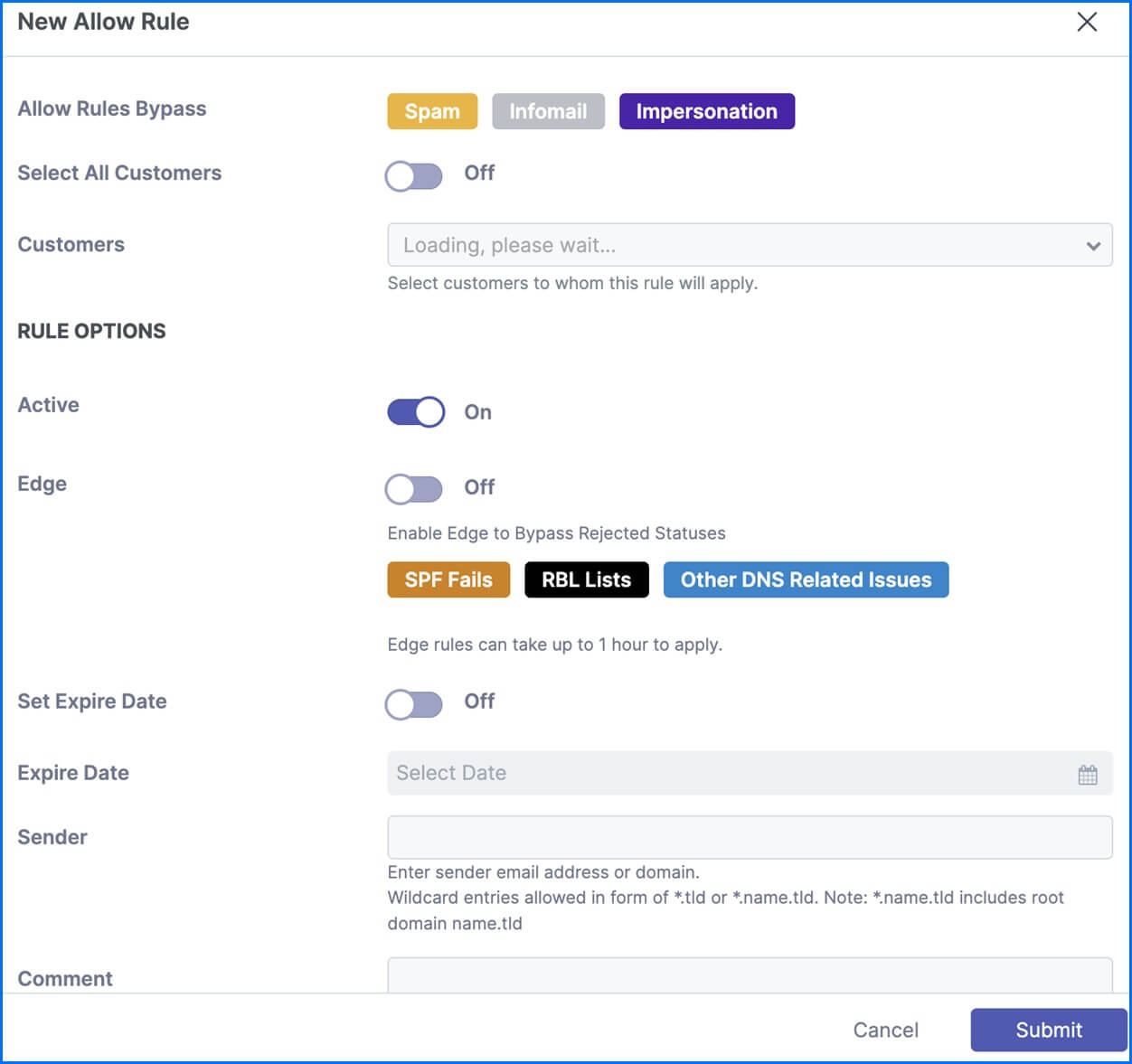 |
Allow rules focus on trusted sender addresses and domains to streamline delivery. For example, you may see senders with misconfigured SPF or DKIM settings. These errors can result in legitimate emails being quarantined. You can create allow rules for high-priority senders to prevent these problems. To maintain a strong security posture, these rules never bypass critical verdicts like phishing, malware, or banned attachments. You should utilize a custom rule when a total exception for these categories is required.
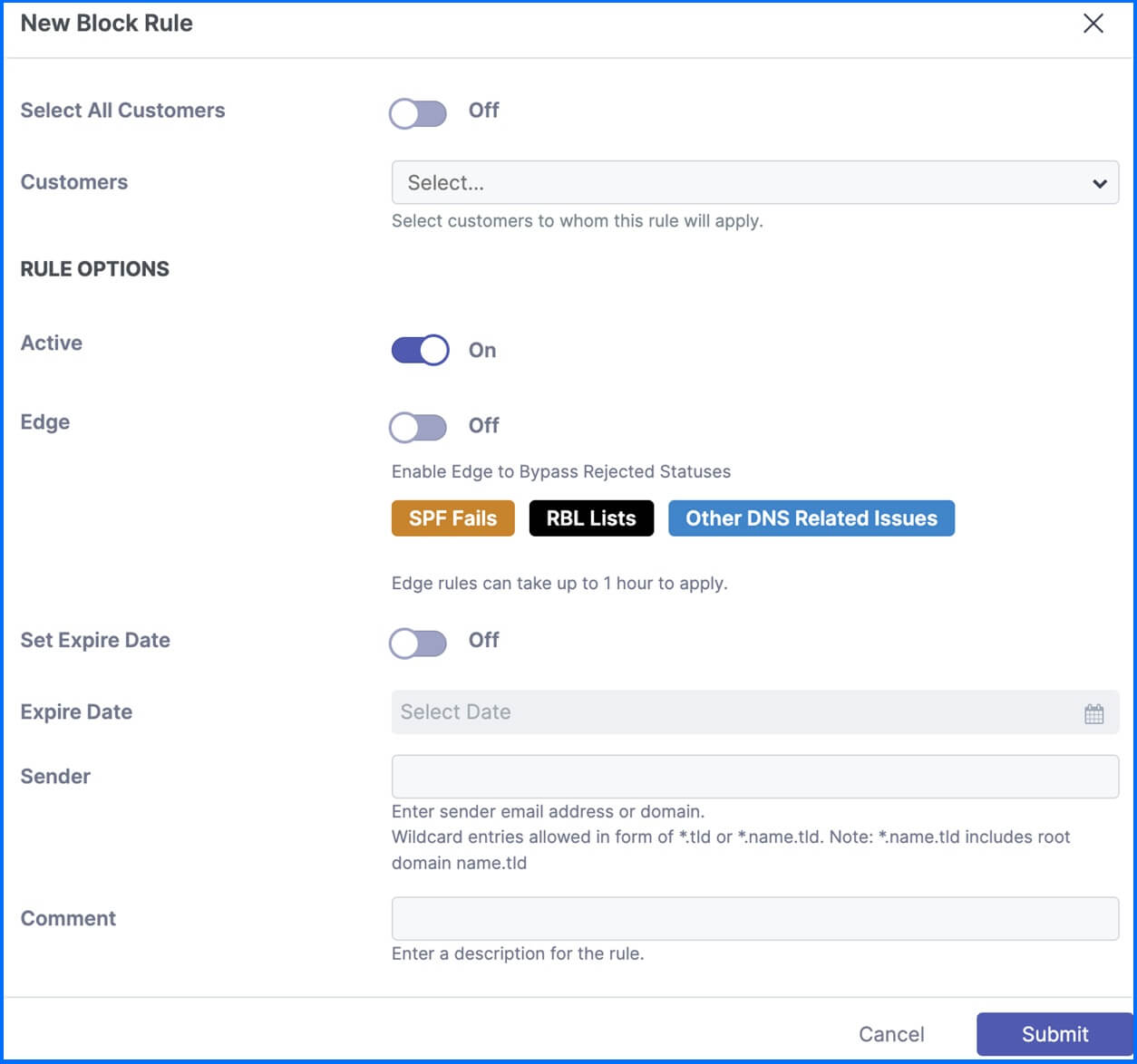 |
Block rules allow you to block emails from a specific sender address or domain. You can apply block rules globally, organizationally, or at the domain and user levels.
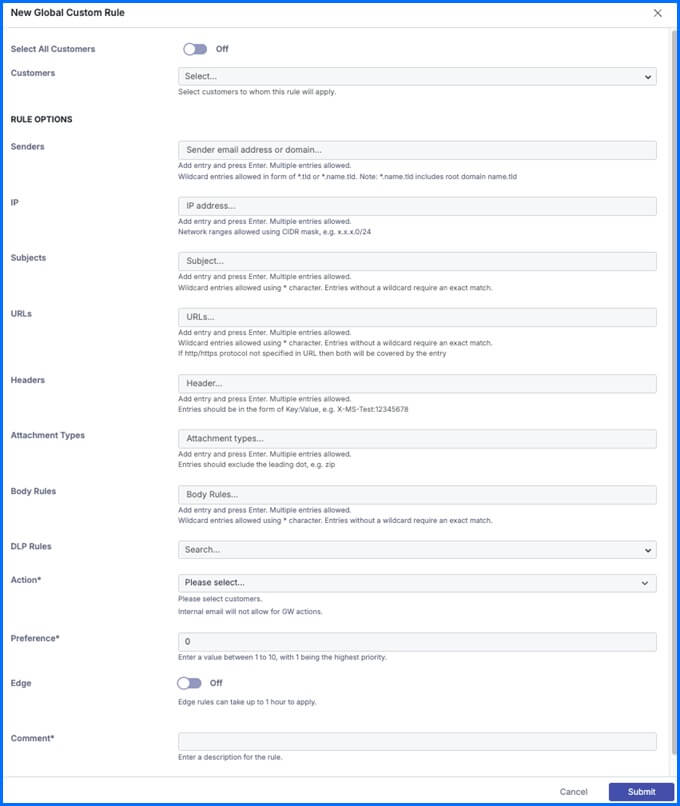 |
Custom rules are your most flexible tool for incident response. You use them when a scenario requires more than a simple allow or block decision. Unlike standard rules, custom rules support multiple conditions in a single entry. You build these using sender addresses, IP ranges, subject lines, URLs, and headers. You even create rules for particular attachment types. This approach allows you to build complex configurations that standard rules cannot handle. For example, organizations using security awareness tools often need to whitelist specific IP ranges. You can enter these addresses in CIDR notation within a custom rule to ensure simulated phishing tests are delivered correctly.
Detailed information about rules configurations can be found at our Bitdefender Support Center here.
Detailed information about Policy & Rule Hierarchy can be found at our Bitdefender Support Center here.
Post-Delivery Remediation and Managed Quarantine
The final layer of your defense focuses on remediation and end-user empowerment. You protect your organization from weaponized threats through the Auto-Remediation feature. This function is available if you use the 365 or Unified deployment models. It continues to monitor emails for 48 hours after they have been delivered. This is critical for catching threats like URLs that were initially clean but are later identified as malicious.
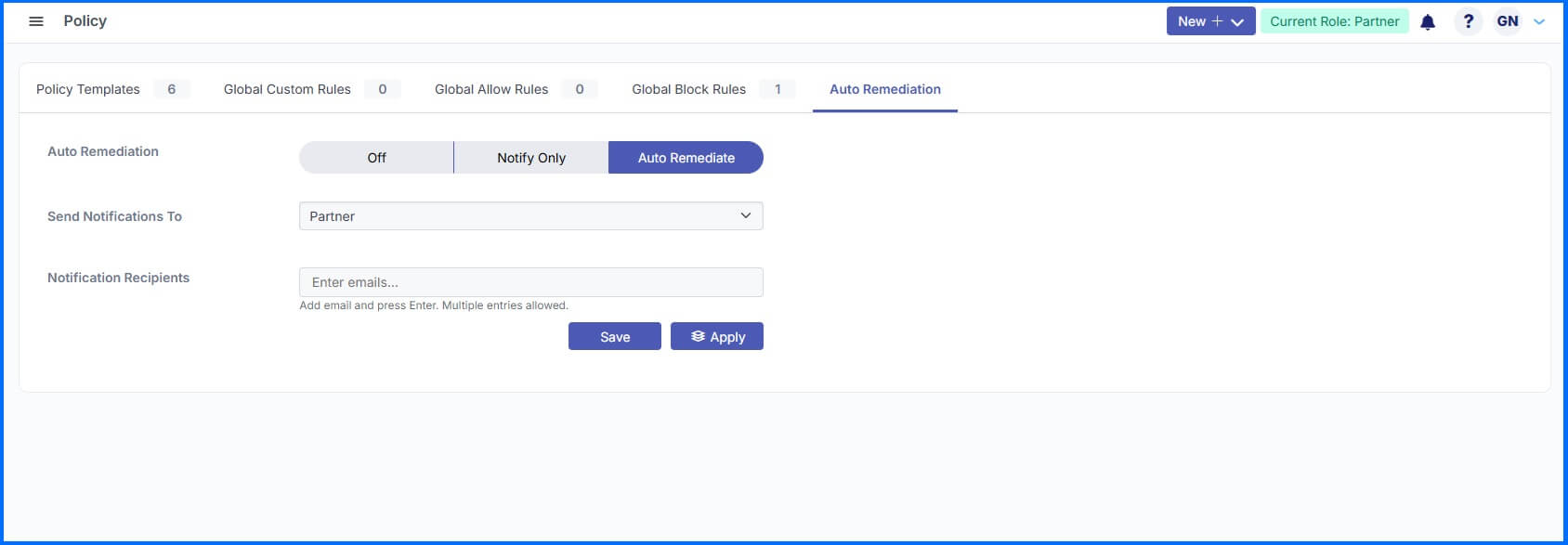 |
You can configure this feature with one of three distinct settings:
Off: This disables both the notifications and the auto-remediation feature.
Notify Only: The system sends an email alert with details about the threat. You must then manually remediate the message using the Live Email Tracker.
Auto Remediate: The system sends an email alert and automatically removes the malicious email from the mailbox.
You can direct these notifications to your customer-level administrators or to specific addresses defined at the partner level.
The Remediate function also acts as a powerful incident response tool for MSPs. This feature allows you to remove specific emails across multiple tenants at the same time. Within 30 seconds, you can resolve an incident for all your customers. This ensures you can neutralize emerging threats before they impact your entire client base.
Quarantine Management
Emails remain in the quarantine for 28 days. You cannot remediate or release messages once they exceed this period. Automated email digests empower your end-users to manage their own low-risk mail. You can enable or disable these digests globally at the MSP level, per customer, or for specific mailboxes. You can configure the frequency and select which email types appear in the reports.
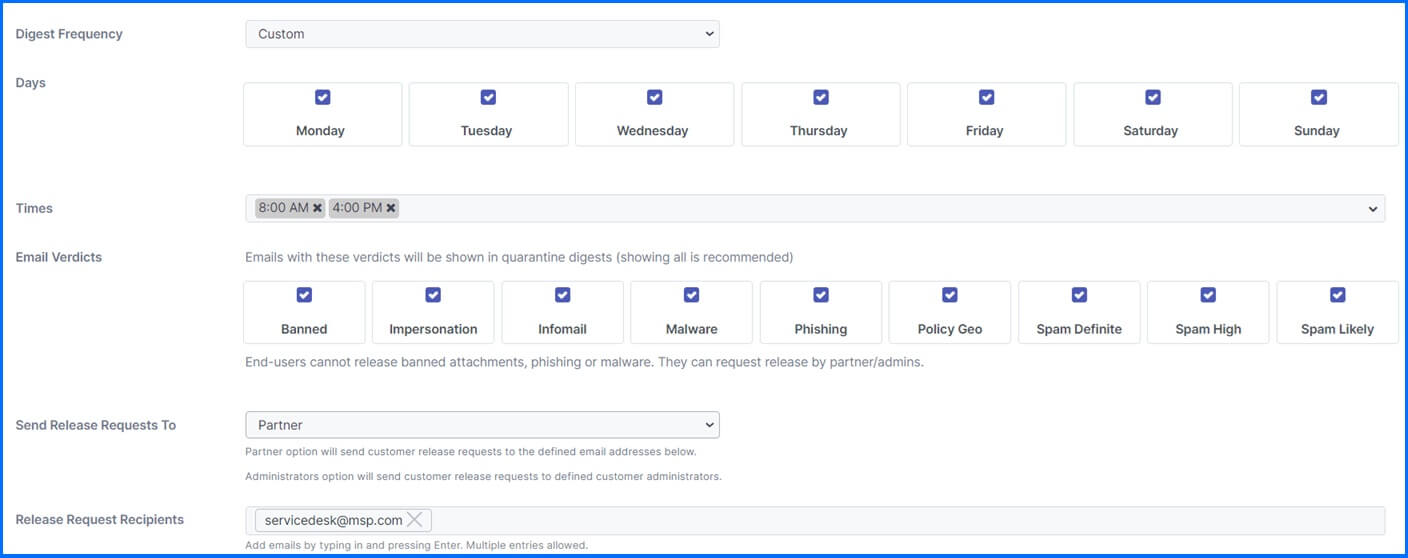 |
Users only receive a digest if the system identifies new quarantined emails since the last summary. If a user wants to check for new information immediately, they can use the digest on demand option. This manually triggers a fresh digest with the latest information. When a user requests an email release, you control where the notification is sent. Emails awaiting approval show a pending status in the Live Email Tracker.
The digest includes options to deliver, delete, or preview messages. The preview button allows users to read quarantined emails safely within a browser window. The system removes all images and converts all links to plaintext. Users can also select the Manage Your Quarantine button to log into a dedicated portal. They sign in using local credentials or Microsoft SSO. In this portal, users view a personal Live Email Tracker for their own addresses. They can also manage their personal policy page to create and edit allow or block rules.
Exchange Protection
Bitdefender Security for Exchange provides a comprehensive suite of security features, seamlessly integrated with Microsoft Exchange Server. These features encompass antimalware, antispam, antiphishing, as well as attachment and content filtering. The main objective is to create a secure messaging and collaboration environment while simultaneously boosting productivity.
Bitdefender Endpoint Security Tools with an Exchange role can be installed on Microsoft Exchange Servers to protect Exchange users from email threats. Customers can install BEST on any number of Exchange servers if the number of active mailboxes adheres to the license limit.
Security for Exchange automatically integrates with the Exchange Servers, depending on the server's role. For each role, only the compatible features are installed, as described here. During installation, the built-in Exchange Antimalware agent is automatically disabled to avoid undesirable outcomes. It is also advisable to disable any other third-party antimalware/filtering agents already installed on the server to avoid any performance problems on the server. The server may experience a storm-like effect caused for example by file scanning at the same time by both solutions.
The Bitdefender Exchange Protection module integrates with Microsoft Exchange Server through transport agents in order to filter the email traffic for malware, spam, and custom attachment & content detection rules (transport level filtering). A scan can also be done on demand to check all incoming, internal, and outgoing emails. Administrators can create content filtering rules utilizing regular expressions to scan the body and subject of the message to catch email matching criteria based on compliance with regulations such as ID number or insurance number.
 |
One of the most important functionalities is related to Domain IP which allows detecting spoofed emails and thus increases protection. Admins should use this feature to prevent their own domains from being spoofed. Sophisticated usage of domain spoofing may lead to money stealing, for example impersonating email communications between fake CEO and financial department.
Further elaboration on the antispam functionality is provided below in the section Bitdefender Antispam service, where detailed information about its usage and implementation is described. The same engine is utilized for both Exchange and Email protection, ensuring consistent and reliable security measures.
The Exchange quarantine contains both emails and attachments. While the Antimalware module quarantines only email attachments, the Antispam, Content, and Attachment Filtering modules quarantine the entire email. All reports related to Blocked Content and Attachments, Email, and Malware Activity are accessible to the administrator from the GravityZone console.
Detailed information about Security for Exchange configurations can be found at our Bitdefender Support Center here.
Endpoint-Level Email Protection with BEST
While dedicated email security solutions like Security for Email and Exchange Protection are crucial for filtering threats at the mail server or gateway, the Bitdefender Endpoint Security Tools (BEST) agent, installed on individual user devices, provides an additional layer of security directly at the endpoint.
The BEST agent's capabilities include email protection, managed through the Network Protection module in Web Protection section of its policy configuration. This functionality supports common email protocols such as POP3, SMTP, IMAP, and MAPI, allowing for the monitoring and securing of various types of email traffic. To enable scanning of encrypted MAPI traffic, MAPI interception must first be activated in the General settings of the policy.
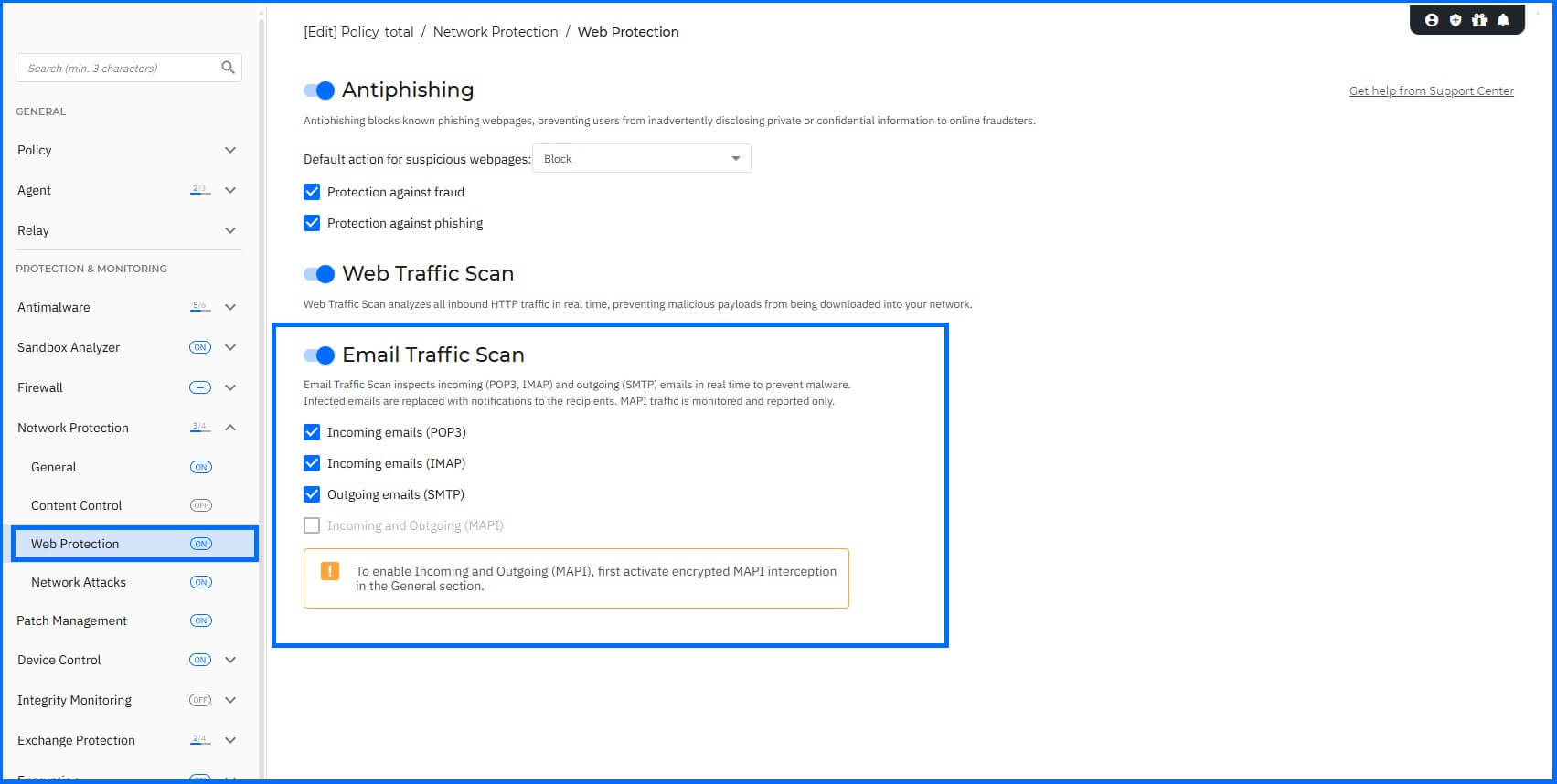
Incoming emails (via POP3, IMAP, and MAPI) and outgoing emails (via SMTP and MAPI) are scanned in real time. This process aims to prevent malware from being downloaded to the endpoint from incoming messages and to stop infected files from being transmitted to other devices through outgoing communications. When infected emails are detected via POP3, SMTP, or IMAP, BEST replaces these messages with notifications to the recipients. For MAPI traffic, the system monitors and reports detected threats without replacing the email content.
It's important to recognize that while endpoint protection is a critical component, stopping threats before they reach the endpoint remains a primary objective. A multi-layered security strategy, combining endpoint protection with server and gateway-level defenses, helps reduce the attack surface and provides a more robust defense.
Bitdefender Antispam Service
The Bitdefender Antispam service provides a multi-layered defense designed to neutralize email threats before they reach the inbox. By combining traditional filtering with predictive, AI-driven technologies, the engine efficiently detects email threats across global languages while maintaining an industry-leading low false-positive rate.
Bitdefender’s email security technologies are utilized across the GravityZone platform, Exchange protection modules, and as a specialized Email Threat Protection SDK for OEM partners. Consistently earning Virus Bulletin’s highest certification (VBSpam+) since 2015, Bitdefender Antispam engine maintains detection rates exceeding 99.9% and is integrated into the security stacks of numerous technology vendors worldwide.
Architecture and Cloud-Powered Detection
At its core, the technology operates as a high-performance, cloud-native scanner. Rather than relying on resource-intensive local processing, the engine extracts relevant metadata from MIME files and transmits it via an SSL-secured connection to the Bitdefender Cloud.
This architecture ensures:
Minimal Footprint: Local resource consumption is limited to a few megabytes of memory.
Lightning-Fast Verdicts: Results, threat context, and probability scores are returned in milliseconds.
Global Intelligence: Continuous training on diverse, language-independent threat feeds ensures protection against localized and international campaigns.
Advanced Filtering & Detection Engines
The Bitdefender engine employs specialized filters that move beyond simple keyword matching to perform deep contextual analysis.
 |
Reputation and Contextual Intelligence
IP, Domain, and URL Reputation: Leverages real-time blacklists and contextual threat intelligence to block known malicious senders and map active spam campaigns as they emerge.
Email Address & Phone Number Filtering: Targeted blocklists identify known spamming accounts and fraudulent phone numbers used in dating scams and financial fraud.
Cryptocurrency Wallet Blacklists: Proactively targets extortion and "sextortion" scams by identifying obfuscated wallet addresses.
Content Analysis and Deobfuscation
Patented Fingerprinting Algorithms: Utilizing cryptographic hashes and HTML fingerprinting, the system analyzes email structures, headers, and body content to identify unique "fingerprints" of spam campaigns, even when content is slightly varied.
AI-Powered Image Analysis: The Antispam service employs computer vision to detect spam and phishing triggers embedded in images, a common technique used to bypass text-based filters.
Malicious Attachment Detection: A critical sub-layer that identifies weaponized documents and phishing payloads before execution.
Predictive Heuristics and Machine Learning
Deep Learning Models: Proactive detection is driven by AI models trained on vast datasets of malicious and benign emails. These models recognize the subtle hallmarks of Spear Phishing and Business Email Compromise (BEC) by inspecting "From" and "Reply-to" header anomalies.
Proactive Heuristics Engine: Combines pattern recognition with heuristic filters to identify new, obfuscated campaigns that have no signature.
Threat Classification and Verdicts
The service provides more than a binary "spam or clean" result. Through machine learning classification models, it delivers a detailed bitmask verdict that categorizes the threat for more granular security orchestration. This enables security teams and automated systems to accurately prioritize and respond to emails based on specific classifications:
Phishing (including BEC)
Malware
Scam & Extortion
Marketing
Clean/Legitimate
By providing a threat probability score alongside these categories, Bitdefender enables an adaptive security posture, allowing organizations to tune their email protection sensitivity.
Recommended Content
To learn more about the technologies behind the Protection layer, we recommend reading the next article Network Protection.
More Resources
GravityZone Extended Email Security official website: Bitdefender GravityZone Extended Email Security
GravityZone Extended Email Security Guided Tour: Extended Email Security Guided Tour
GravityZone Security for Exchange Servers official website: Bitdefender GravityZone Security for Exchange
GravityZone Security for Exchange Servers Guided Tour: Security for Exchange Servers Guided Tour
Discover the Email Security full potential with our dedicated video masterclasses: Masterclass